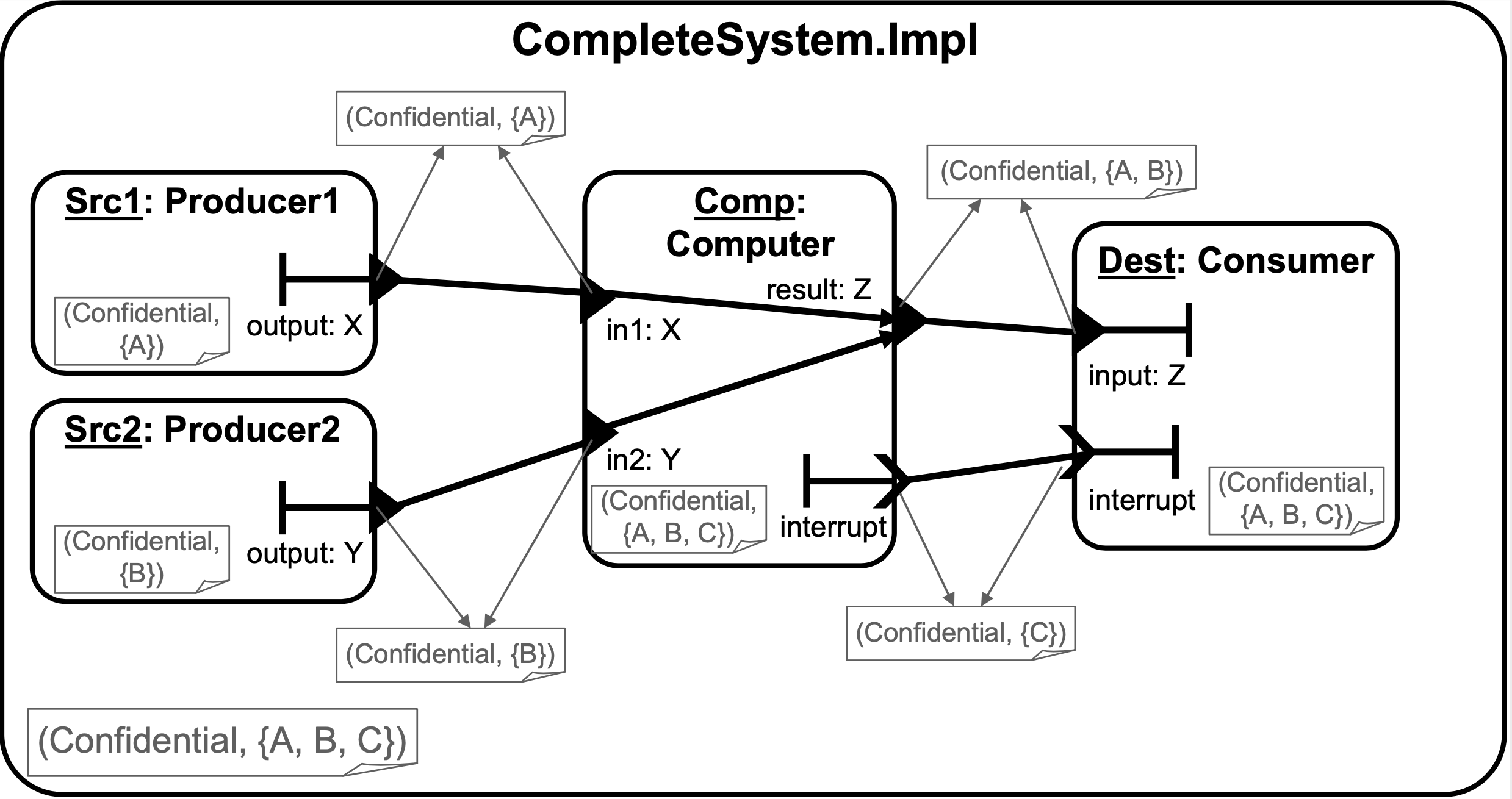
Scalable and secure access control policy for healthcare system using blockchain and enhanced Bell–LaPadula model | SpringerLink
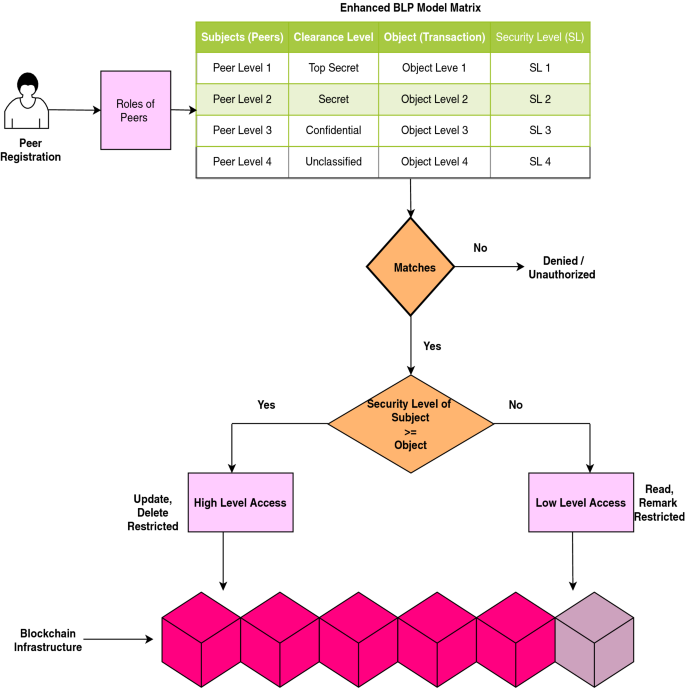
Scalable and secure access control policy for healthcare system using blockchain and enhanced Bell–LaPadula model | SpringerLink
Evaluation of the Appropriateness of Trust Models to specify Defensive Computer Security Architectures for Physical Protection S

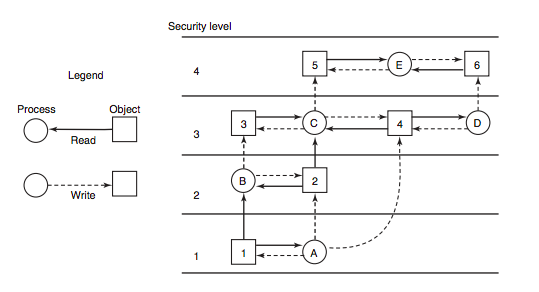
Example scenarios of a (a) DAC; (b) Bell-LaPadula; (c) Brewer-Nash; (d)... | Download Scientific Diagram
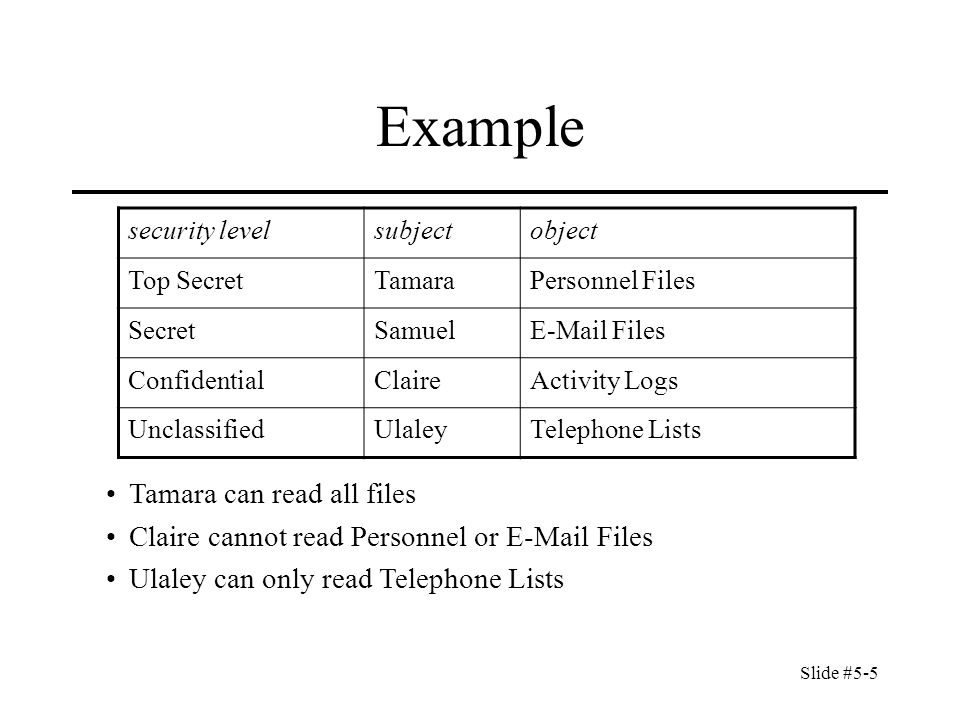
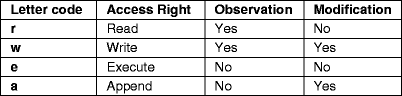
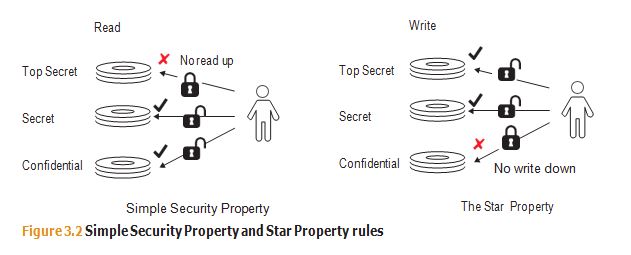
Slide #5-1 Chapter 5: Confidentiality Policies Overview –What is a confidentiality model Bell-LaPadula Model –General idea –Informal description of rules. - ppt download


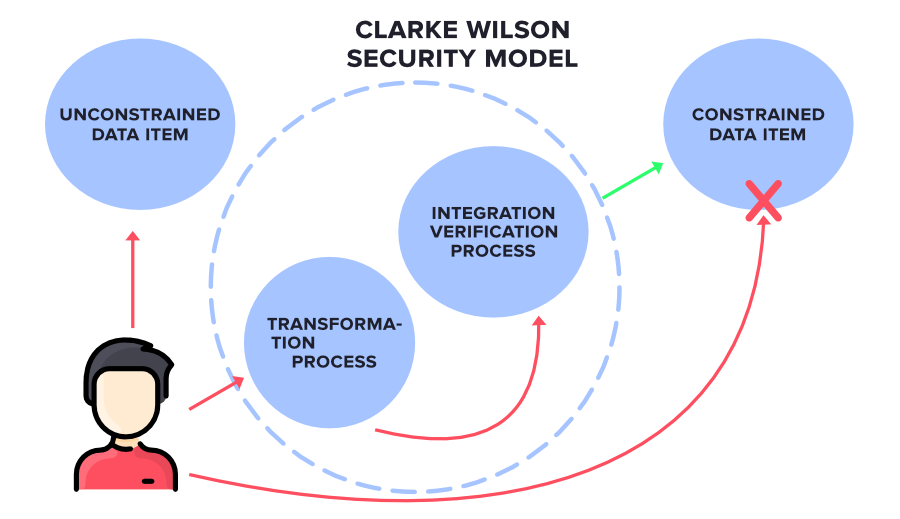



![Information Security Series: [Part2] Principles of Privileges Information Security Series: [Part2] Principles of Privileges](https://cdn.hashnode.com/res/hashnode/image/upload/v1647290827356/3qC3AeROC.png?auto=compress,format&format=webp)