TRM Analysis Corroborates Suspected Ties Between Conti and Ryuk Ransomware Groups and Wizard Spider | TRM Insights
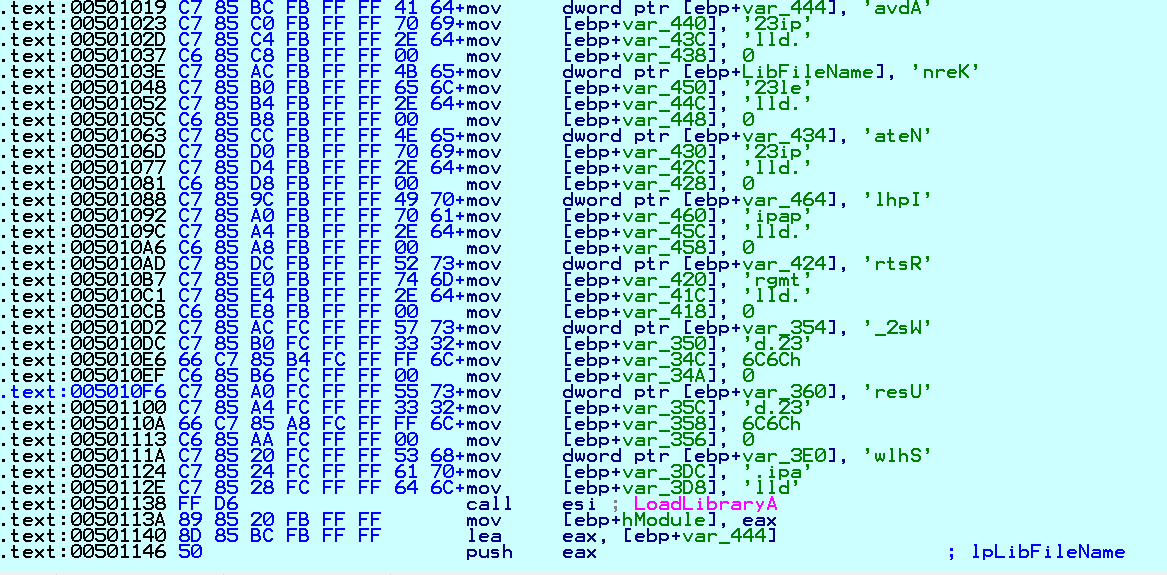
GitHub - j91321/conti-manuals-analysis: Analysis of techniques used by Conti ransomware affiliates from their leaked manuals.
GitHub - j91321/conti-manuals-analysis: Analysis of techniques used by Conti ransomware affiliates from their leaked manuals.


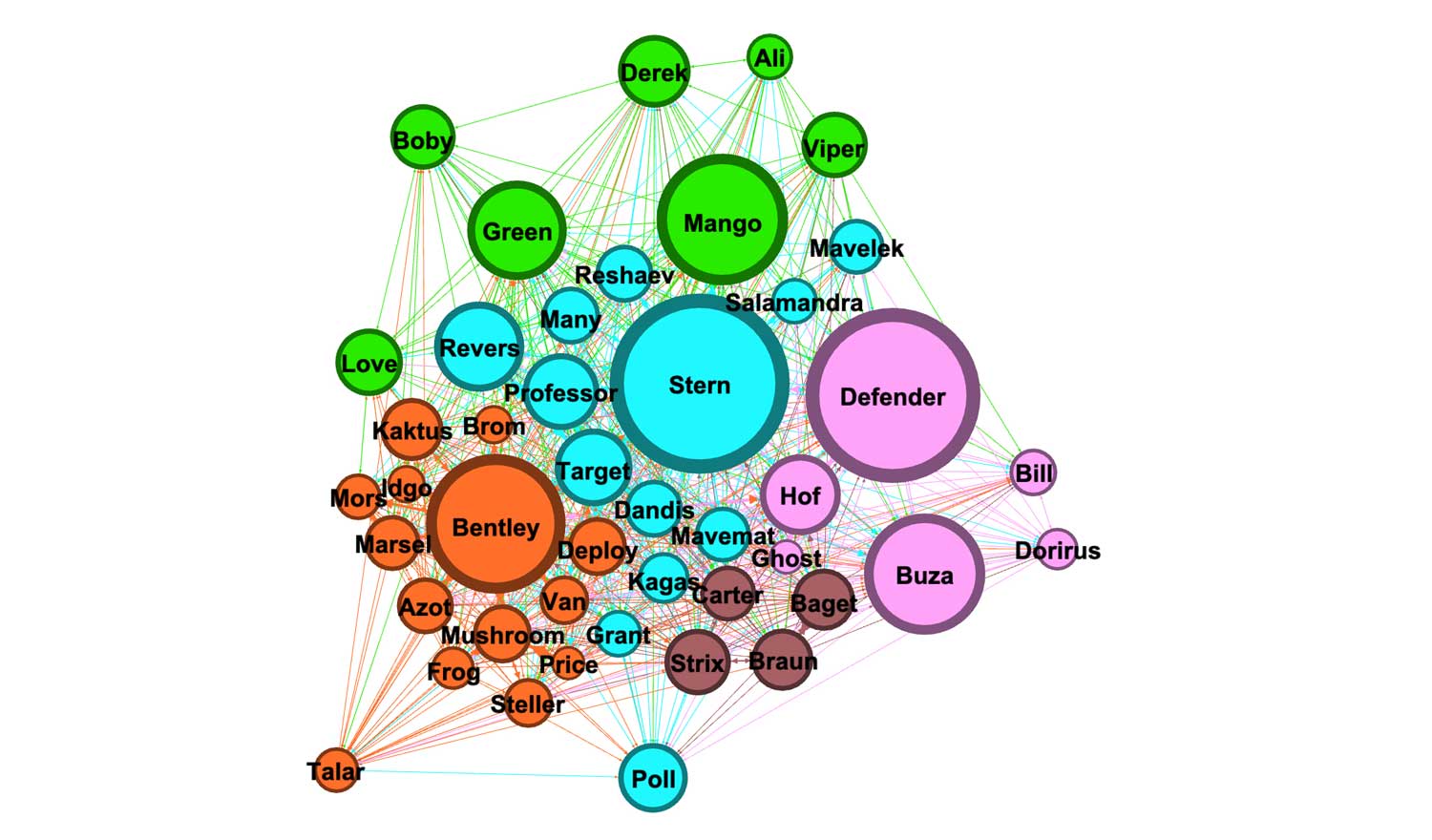
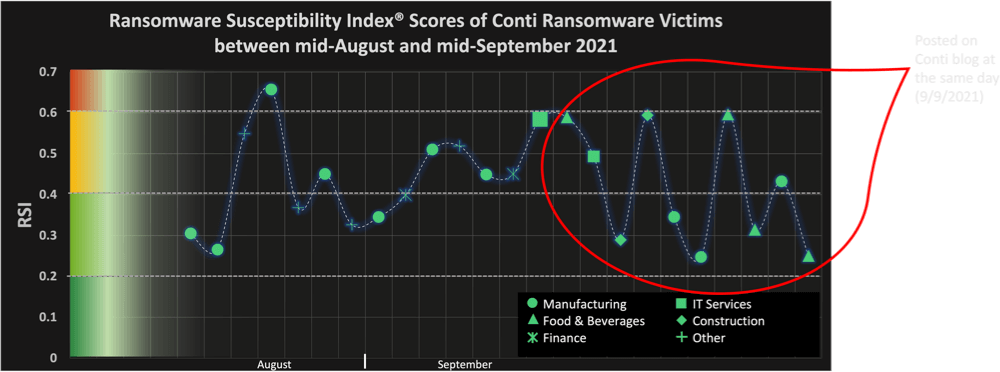
![CONTI] Ransomware Group In-Depth Analysis - PRODAFT CONTI] Ransomware Group In-Depth Analysis - PRODAFT](https://www.prodaft.com/m/resource/conti.jpg)