GitHub - voidregreso/HashBull_GUI: Official Hashbull source code with compilation issue revises, and binaries included.

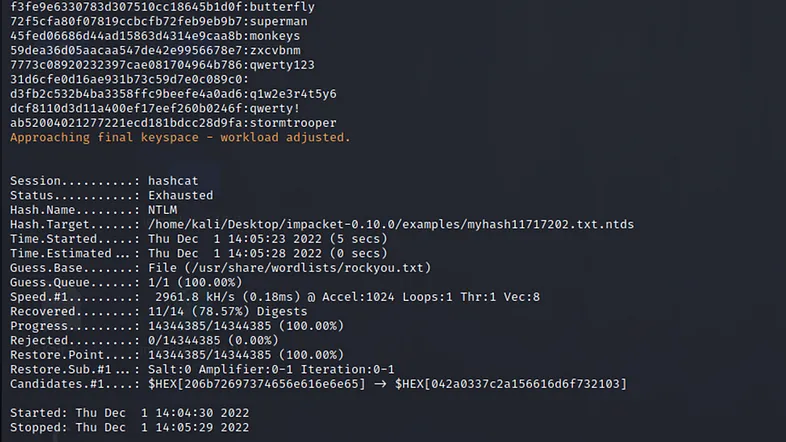
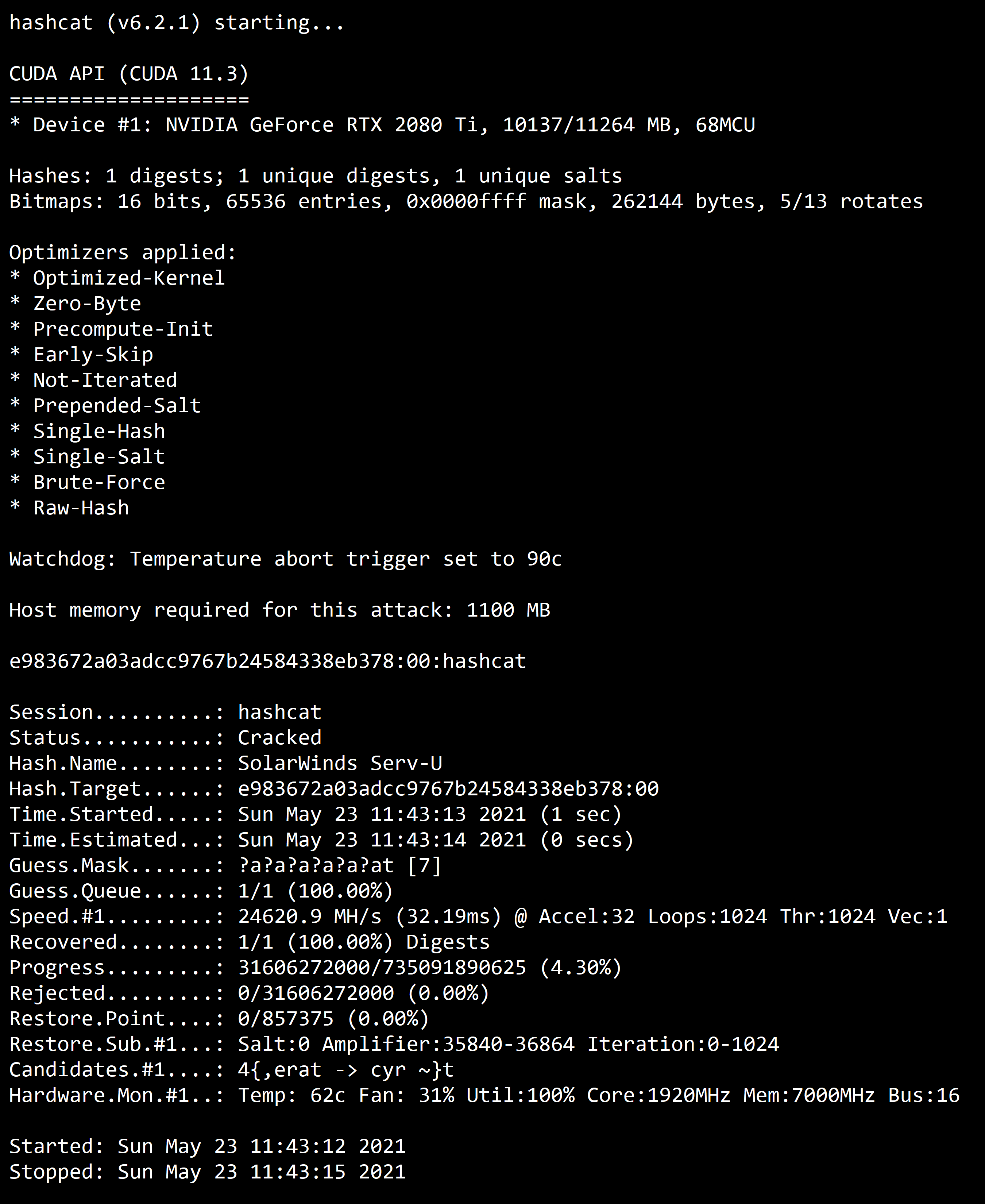
hashcat on Twitter: "Support for PKZIP Master Key added to #hashcat with an insane guessing rate of 22.7 ZettaHash/s on a single RTX 2080Ti. All passwords up to length 15 in less
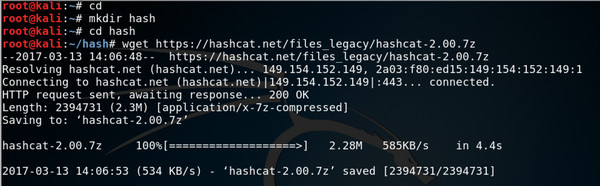
GitHub - philsmd/7z2hashcat: extract information from password-protected .7z archives (and .sfx files) such that you can crack these "hashes" with hashcat